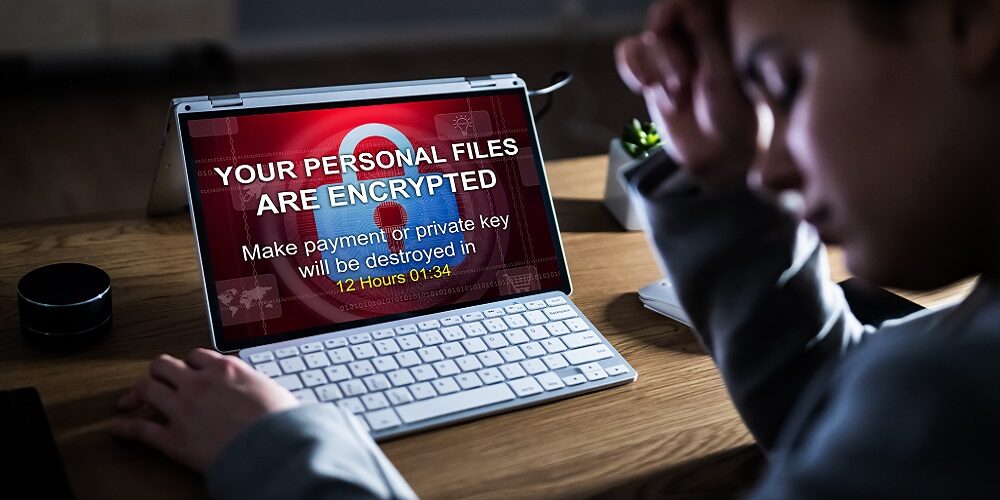
Ransomware payments have skyrocketed in recent months, hitting an average of over $300,000 in the last quarter of 2021, as the risks of doing business has increased for ransomware threat actors, according to a new report.
Coveware, a ransomware recovery firm, reports that the average ransomware payment in the fourth quarter was $322,168, a 130% increase from the previous quarter. Meanwhile, the mean ransom payment was $117,116, a 63% bump from the third quarter.
The company says this reflects a “subtle tactical shift’ in the ransomware-as-a-service economy that reflects increasing costs and risks associated with cybercrime, including increasing law enforcement attention.
As noted by Coveware, 14 members of the REvil ransomware gang were arrested by Russia’s FSB last month in a raid that resulted in seizing about $7 million in combined currencies and 20 luxury cars.
“This was an unprecedented action for the Russian government to take and has surely increased the risk profile of being a ransomware affiliate,” the company wrote in the report. “This decreases the addressable market of cyber criminals willing and able to execute these attacks, as not all of them are willing to risk jail time or western extradition for the money they earn.”
Due to that increased risk, ransomware actors are increasingly targeted larger companies that have the means to pay a “big game” ransom amount, but small enough to keep attack operations costs low and avoid media and law enforcement attention.
The tactical shift involves a deliberate attempt to extort companies that are large enough to pay a ‘big game’ ransom amount but small enough to keep attack operating costs and resulting media and Law Enforcement attention low.
The company found that the proportion of victims with between 1,000 and 10,000 employees grew from 8% in the third quarter to 14% last quarter, and the average ransom payment in that group was “well north” of $1 million.
In addition, the world is just getting better at cybersecurity, the report suggests, as cyber insurance providers are mandating better security in order to maintain policies, high-profile attacks are spurring awareness, and government agencies are becoming more involved in cybersecurity—all of which is leading to more expenses and risk for cybercriminals.
The report also found an increase in the percentage of ransomware actors maintaining persistence in victim systems, as 82% of attacks had persistence tactics, techniques and procedures (TTP).
For initial ingress vectors, remote desktop protocol compromise and email phishing remain the top two, but software vulnerability exploiting is rising, with two 2021 Microsoft Exchange vulnerabilities (CVE-2021-34473 and CVE-2021-26855) and a 2018 Fortinet firewall bug (CVE-2018-13379) the most exploited by ransomware actors.
If you enjoyed this article and want to receive more valuable industry content like this, click here to sign up for our digital newsletters!









Leave a Reply