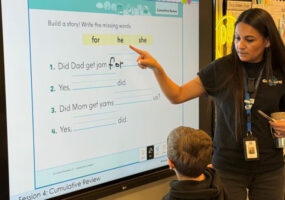
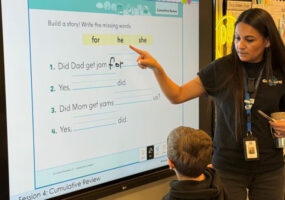
Rose Salgado Elementary Transforms Learning with LG’s Interactive Technology
Rose Salgado Elementary leverages LG’s technology to create a flexible, student-centered, interactive learning environment.
March 20, 2026 TD Staff Leave a Comment
Rose Salgado Elementary leverages LG’s technology to create a flexible, student-centered, interactive learning environment.

February 1, 2026 Alex Halliday Leave a Comment
Editor’s Note: Another version of this article originally appeared on our sister-site Security Sales & Integration on January 28, 2026. It has since been updated for My TechDecisions’ audience. More system integrators are beginning to recognize that IT departments hold greater influence over technology investments that were once managed solely by security teams, particularly when […]

January 20, 2026 Dan Ferrisi Leave a Comment
The BenQ InstaShow WDC15 offers 4K screen mirroring with no software, minimal latency and robust security for classrooms and meetings.

August 4, 2025 Shankar Somasundaram Leave a Comment
Note: The views expressed by guest bloggers and contributors are those of the authors and do not necessarily represent the views of, and should not be attributed to, My TechDecisions. Universities are filling up with network-connected devices. Smart locks manage building access. HVAC systems run on automated controls. Cameras stream to command centers. Vending machines, printers, thermostats, […]

March 20, 2025 TD Staff Leave a Comment
Watch Jim Grass of Singlewire Software discuss mass notification solutions, opportunities for integrators and improving workplace safety.

March 5, 2025 TD Staff Leave a Comment
Catchbox Plus earns high praise from URI’s IT lead Jeffrey Levesque for its reliable, user-friendly design, transforming the campus’s AV solutions.

December 30, 2024 Bruce A. Canal, CPP Leave a Comment
This quick guide will help you navigate and select from the diverse range of security SaaS options available to fit your specific needs.

December 10, 2024 Rafal Komosa Leave a Comment
Technology investment isn’t simply about keeping pace; it’s about setting the foundation to become an effective and efficient innovator.

December 3, 2024 TD Staff Leave a Comment
The Thomas Telford Multi Academy Trust (TTMAT), comprising five schools in the West Midlands, U.K., prioritizes a unique flat management structure, granting Headteachers full autonomy while fostering collaboration to drive educational standards. Committed to enhancing teaching and learning, TTMAT recently overhauled its classroom technology with Avocor displays to create a more engaging and effective educational environment Across […]

October 23, 2024 TD Staff Leave a Comment
Jabra, the global enterprise audio and video solutions provider, released a new study, Great ExpectAItions – Work in the Age of AI, which reveals that while many business decision-makers (84%) express high levels of trust in AI, very few office workers (26%) are using it in their daily roles due to a variety of perceived […]

FREE Downloadable resources from TechDecisions provide timely insight into the issues that IT, A/V, and Security end-users, managers, and decision makers are facing in commercial, corporate, education, institutional, and other vertical markets
View all Guides
Get your latest project featured on TechDecisions Project of the Week. Submit your work once and it will be eligible for all upcoming weeks.
Enter Today!