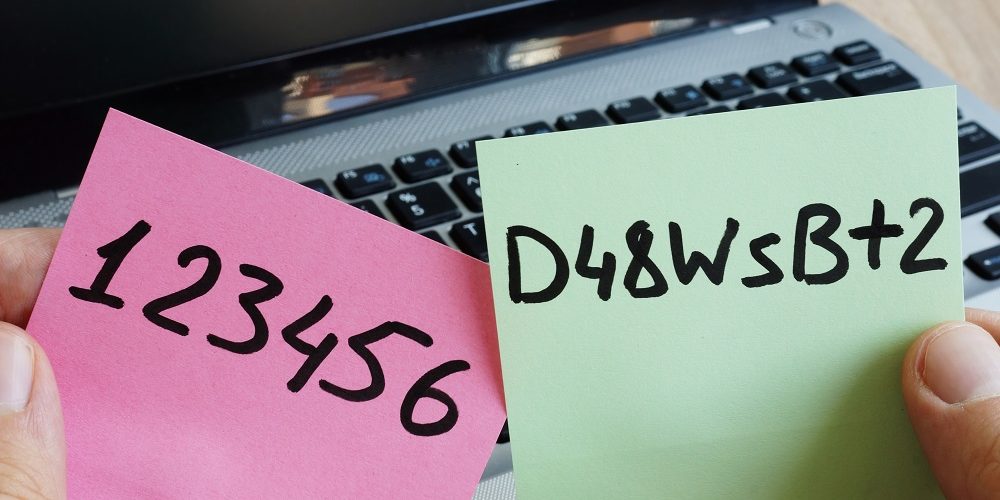
If you’re still requiring users to create complex passwords with a combination of letters, numbers and symbols, think again, says the U.K.’s National Cyber Security Centre.
The NCSC, the U.K. counterpart to the U.S. Cybersecurity and Infrastructure Security Agency (CISA), maintains that complexity requirements and making users regularly change passwords is actually less secure than simply using three random words.
In a new blog, the NCSC says attackers are familiar with complexity strategies, and enforcement of those policies actually results in more predictable passwords.
For example, users typically fall back on previously used passwords and make slight variations, such as replacing the letter ‘o’ with a zero, using different numbers or symbols, and so on. If those pass the password strength meter, users think it’s a secure password.
However, cybercriminals know about those strategies and are adept at guessing passwords based on that criteria.
Instead, the NCSC urges organizations to adopt a password policy of three random words. The agency says this can help users create unique passwords that can be remembered a lot easier than which symbols you added to the end of your overused password.
Listen: My TechDecisions Podcast Episode 129: Moving Past Passwords
According to the NCSC, there are four main reasons why this strategy works:
- Three random word passwords tend to be longer, which lead to a stronger password.
- The technique is easy to understand and simple to explain.
- The concept is new and encourages a range of passwords not previously considered.
- It doesn’t require much effort to remember three random words.
The agency advocates for diversity of password use, meaning reducing the number of passwords that are discoverable by cheap and efficient search algorithms. This forces attackers to run multiple algorithms to recover a useful number of passwords.
However, complex password requirements work against password diversity, leading to to a convergence in strategies and a reduction in password diversity, the agency says. Instead, organizations should use other password strategies that use length rather than character sets to achieve the desired strength, effectively encouraging the adoption of passwords currently unused.
The NCSC says technology will eventually supplement password use — hopefully before hackers catch on to the three random word password strategy.
In a statement, NCSC Technical Director Dr. Ian Levy called traditional passwords with multiple complex passwords “daft.”
“There are several good reasons why we decided on the three random words approach – not least because they create passwords which are both strong and easier to remember,” Levy says. “By following this advice, people will be much less vulnerable to cyber criminals, and I’d encourage people to think about the passwords they use on their important accounts, and consider a password manager.”
If you enjoyed this article and want to receive more valuable industry content like this, click here to sign up for our digital newsletters!









Leave a Reply