A new open-source program called Social mapper was released by Trustwave recently, according to The Verge. The tool is designed for security researchers performing social engineering attacks, and while it is supposed to be used for ethical hacking, the free software is currently freely available.
Social Mapper doesn’t even need access to the social networks, according to The Verge:
Social Mapper doesn’t require API access to social networks, a restriction that has hampered social media tracking tools like Geofeedia. Instead, the system performs automated manual searches in an instrumented browser window, then uses facial recognition to scan through the first ten to twenty results for a match. The manual searches mean the tool can be quite slow compared to API-based scans. The developer estimates that searching a target list of 1000 people could take more than 15 hours.
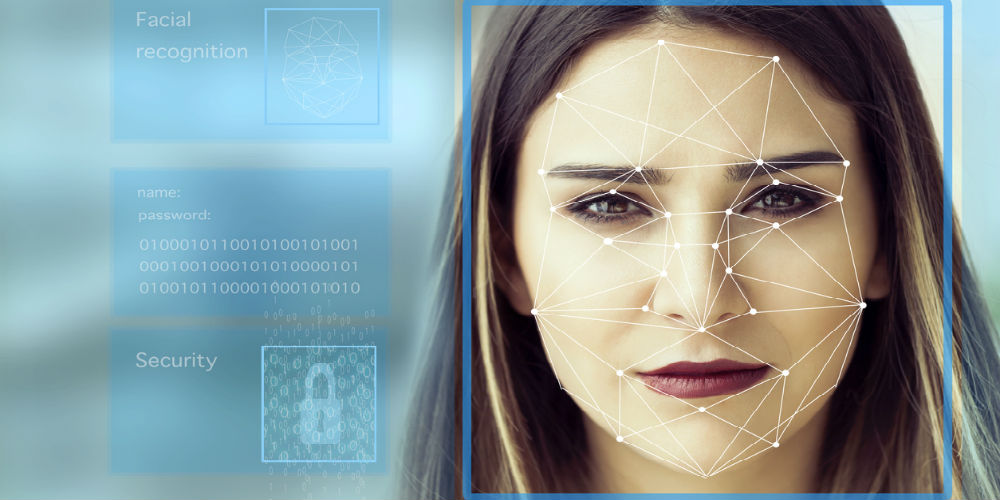
This program comes on the wave of a number of facial recognition developments in the past several months. Amazon’s facial recognition software mismatched 28 congress members, mistaking them for criminal mugshots. The US Army adopted facial recognition technology to detect people using thermal imaging cameras. China is currently testing facial recognition glasses for police officers.
It’s clear that facial recognition software is becoming more prevalent in society. Many groups are lashing out against the practice, especially for governmental use, including the ACLU. The fear is that the data gathered from facial recognition will be used for purposes the public isn’t comfortable with – similar to how Cambridge Analytica used Facebook data to influence voters during elections. Think how facial recognition could identify where people have been, and use that information to track them, predict where they will go, perhaps even blackmail them if the information falls into the wrong hands.
The questions becomes whether or not facial recognition should be allowed, especially in the hands of whoever wants to use that technology. Obviously Trustwave believes anyone should use it – otherwise they wouldn’t have released an open-source technology. However, that same technology could easily be used in phishing campaigns and other attacks. Is that worth it in exchange for intelligence gathering efforts?
It’s a tricky topic, and one that will be debated in the coming years. As legislation passes, consider whether or not facial recognition is something your company would be comfortable implementing – and how would it affect your surveillance efforts?
If you enjoyed this article and want to receive more valuable industry content like this, click here to sign up for our digital newsletters!










Leave a Reply