While the Internet of Things (IoT) is “one of the most transformative innovations of our time,” and is an easy step to connecting together endless devices, ReadWrite says it’s an easy target for unwanted data collectors. Blockchain could be the solution to the problem.
With IoT, the ability for the government and hackers to put their fingers into end users’ and businesses’ data is like fishing in a barrel: “All of our connected devices continuously broadcast our information, and the collection can be used in unimaginable ways…With all the data shared through IoT, it’s almost like surveillance projects…have the ability to bend time and space to repeat the past,” ReadWrite says.
However, ReadWrite reports that progress in developing block chain technology is making IoT more secure, and improving users’ privacy on the World Wide Web.
What decision makers need to know:
For decision makers looking for ways to keep their business’s and personal data protected, they should consider the three main ways blockchain technologies work to boost security:
- Decentralizing the network
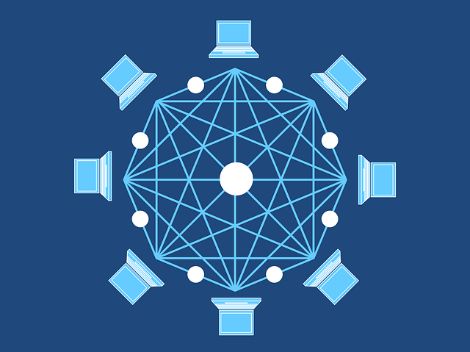
With IoT, devices talk to each other through millions of miles worth of internet infrastructure; since these devices broadcast through centralized servers, weak spots are easily identified by hackers. However, ReadWrite says that blockchain runs a decentralized ledger system, “which distributes information across a network of computers and uses a consensus algorithm to ensure parity.” This means that the information passed through the network isn’t managed by a central authority, and isn’t visible to threats in a central location; instead, the information is spread out, and harder for threats to kick in.
- Tokenized information is enabled
According to ReadWrite, “blockchain was initially conceived by bitcoin developers to facilitate p2p transactions without the use of an intermediary like a bank,” and this “tokenized” technique has been successful so far. The same technique can be applied to IoT – “tokenized information is the perfect balance between accessibility and privacy.” For IoT, tokenized information can act as a substitute for a person’s or business’s actual information. As a result, this can achieve a personal connection without revealing key data, thus keeping the actual data secure.
- Blockchain is unchangeable
ReadWrite says that blockchain technologies offer a transparent framework that records activity, and prevents activity from being tampered with. This characteristic is key in making sure that users’ and businesses’ data is “accurate, intact, and secure.” This also prevents whistleblowers and hackers from creating a data breach, and keeping their moves hidden and unsolvable during an investigation.
If you enjoyed this article and want to receive more valuable industry content like this, click here to sign up for our digital newsletters!









Thanks For Giving the Great information about the Blockchain
Great breakdown and concise summation of what can easily be a very complicated and confusing topic .
Gonna read this a few more times to make sure it sticks.
Inspirational content, have achieved a good knowledge from the above content on Blockchain Training useful for all the aspirants of Blockchain Training.