Passwords. Let’s talk about ‘em. I’ve forgotten some. You have too. No big deal. Just click the forgotten password link and follow the steps. Hopefully you remembered which email address you used to set up the account.
But the code to unlock your phone? You can probably do that in your sleep. Chances are it’s something to do with your birthday, pet, child or spouse.
Easy-peasy, right? Happens to everyone.
But let’s say you’re in a very high-profile government position, or even the president’s personal lawyer. You better not open yourself up to that kind of vulnerability.
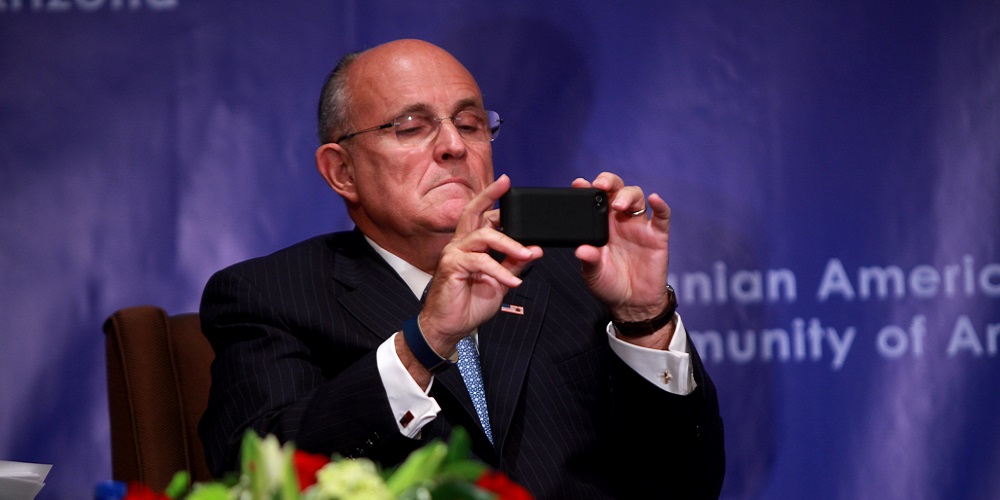
I bring you Rudy Giuliani, who has done just that.
Less than a month after he was named President Donald Trump’s cybersecurity advisor in 2017, he brought his iPhone into an Apple store.
That’s right. Who knows how many government secrets and classified information was on that thing.
According to news reports, Giuliani was locked out of the device because he forgot the passcode and entered the wrong one at least 10 times, which automatically locks the device.
Even before he held that position, the former mayor of New York City worked for the cybersecurity practice of international law firm Greenberg Traurig. He left that post to devote more time to Trump’s defense team as several investigations were mounting.
Read Next: Apple Now Fine with Independent Shops Repairing iPhones
Giuliani’s tech missteps are fairly well documented, it turns out.
He once created a URL during a Twitter rant and just recently butt dialed reporters.
Here are some really simple iPhone security tips that even Rudy can take advantage of:
- Lock your phone when it’s in your pocket or when you aren’t using it. Last I checked, your glutes don’t have the dexterity of your hands, and the phone should stay locked.
- Disable lock-screen notifications. It doesn’t make much sense to lock your phone but have sensitive information available for all to see.
- Make your phone automatically lock sooner. You can make the device lock almost immediately after using it last, which is helpful in the event you leave it behind in a restaurant or on the train. What use is a locked phone to someone who picks it up?
- Disable Siri on a lock screen. This wonderful personal assistant actually spoiled a birthday surprise for my wife earlier this week. She’s a treat and sometimes helpful, but a blabbermouth.
- Turn on automatic updates. New updates bring along new security patches to prevent crashes or theft.
If you enjoyed this article and want to receive more valuable industry content like this, click here to sign up for our digital newsletters!









Leave a Reply